How to configure the firewall on Ubuntu using UFW (Uncomplicated Firewall)
Posted in "News"Ubuntu firewall
Source:https://help.ubuntu.com/community/UFW
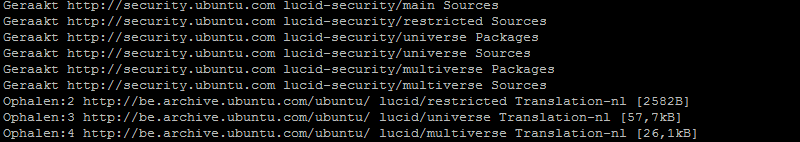
The default firewall configuration tool for Ubuntu is Ufw and stands for "Uncomplicated Firewall". It was developed to ease ip-tables firewall configuration, and provides a user friendly way to create an IPv4 or IPv6 host-based firewall. Ubuntu already has a very good tutorial on how to use Ufw which your can find here. I only tried to make it a bit clearer for you using some examples and the port numbers listed. Happy configuring!
1. Start Ufw.
Ufw by default is initially disabled. So it needs to be enabled on first use.
sudo ufw enableIf you want to disable it again, use this command:
sudo ufw disableBy default, Ufw denies all incoming traffic but allows all outgoing traffic, so you will need to open the ports you want to allow. Check your applications and which ports will need to be opened.
2. Port numbers.
If you don't have a clue which port is used for which application, just take a look in the port list. Most common ports used are:
| Port | Description |
|---|---|
| 21 | File Transfer Protocol (FTP) |
| 22 | Secure Shell (SSH) |
| 23 | Telnet remote login service |
| 25 | Simple Mail Transfer Protocol (SMTP) |
| 53 | Domain Name System (DNS) service |
| 80 | Hypertext Transfer Protocol (HTTP) used in the World Wide Web |
| 110 | Post Office Protocol (POP) |
| 119 | Network News Transfer Protocol (NNTP) |
| 137 | Netbios Name Service (Used by Samba) |
| 138 | Netbios Datagram Service (Used by Samba) |
| 139 | Netbios session service (Used by Samba) |
| 143 | Internet Message Access Protocol (IMAP) |
| 161 | Simple Network Management Protocol (SNMP) |
| 443 | HTTP Secure (HTTPS) |
| 445 | Microsoft-DS SMB file sharing (Samba) |
3. Allow incoming traffic.
To allow traffic for SSH to your server you need to open port 22. there are serveral ways to do this. The first option is adding the port number:
sudo ufw allow 22Another way is to add the service using the application name:
sudo ufw allow OpenSSHTo see what applications are available on your system, you need to enter this command:
sudo ufw app listDepending on what applications are installed and enabled you will get a list containing all available application names, for example:
- Apache
- Apache Full
- Apache Secure
- Bind9
- OpenSSH
- Samba
Adding Apache will allow all incoming traffic to port 80, adding Apache Secure will allow all incoming traffic to port 443 for HTTPS,...
If you have samba installed you could allow all incoming traffic by adding:
sudo ufw allow 137
sudo ufw allow 138
sudo ufw allow 139
sudo ufw allow 445Or you can simply allow all incoming traffic to Samba using:
sudo ufw allow SambaOr if you only want to allow incoming traffic from hosts within the local network (assuming your IP addresses are in the 192.168.1.x range):
sudo ufw allow from 192.168.1.0/24 to any app SambaOr if you want to allow only tcp traffic to a port for a network range:
sudo ufw allow from 192.168.1.0/24 to any port 445 proto tcp
4. Deny incoming traffic.
Deny incoming traffic to OpenSSH:
sudo ufw deny 22or
sudo ufw deny OpenSSH
5. Removing rules.
Deleting rules can be accomplished by:
sudo ufw deleteexample, on how to delete deny rule for port 22:
sudo ufw delete deny 22or if given by application name:
sudo ufw delete deny OpenSSHor by rule number (look at "6. Check the configuration - numbered view of all rules") :
sudo ufw delete
6. Check the configuration.
To see the firewall status, enter:
sudo ufw statusAnd for more verbose status information use:
sudo ufw status verboseThis will give you the port numbers if you used the application names when adding rules. It's also possible to get a numbered view of all rules
sudo ufw status numbered The numbers can also be used when removing rules ("5. Removing rules - delete by rule number").
7. Logging traffic.
Logging traffic can be useful to recognise hacking attempts, but logging is disabled by default so you need to turn this on:
sudo ufw logging onTo turn it off again, use:
sudo ufw logging offThe firewall logs will show up in three different log-files in the standard log directory "/var/log".
Check them using the tail command:
tail -f /var/log/message
tail -f /var/log/syslog
tail -f /var/log/kern.log